In this article I will help you to understand, how to recover your entire forest from total lost. Many networks these days do have multiple domain controllers and especially on enterprise networks losing all available domain controllers less likely but still possible. If you do not have published SOP for recovering your Active Directory Forest the steps in this article might provide you frame work you need.
Scenario: Entire datacenter is gone, you do have your backup and infrastructure ready on the second data center.
Note: backup at least two Domain controller from each domain regularly to preserve better recovery option when needed.
Note: per Microsoft it is not recommended to restore FSMO role holder in the interest of simplicity. (Forest recovery white paper)
now we lost DC1 , and we must recover Entire Forest /Domains from tape backup.
Steps:
- Prepare VM host on the DC2 , ready to be deployed
- Make sure each VM is able to talk to ( TCP/IP) your backup media Servers in the DC2
- Recover first Domain Controller on the Forest Root from good tape backup (SystemState)
- You will need to know DSRM administrator user name and password
- Reboot into DSRM (Directory Services Restore Mode) mode by pressing F8 key after successful restore.
- Install VM host integrated Drivers ( Do not remove any of the existing drivers came with image, it could cause blue screen)
- Disable all Physical NIC cards , un-check option register this connection into DNS on all the NIC’s which are no longer being user. Domain controllers in general do not need more than single NIC.
- Make sure all Disks for the Recovered DC is configured correctly ( SYSVOL and .DIT )
- Bring all Disks online , make sure correct disk labeling is in place ( same as lost DC )
- Verify SYSVOL and .DIT exist after successful recovery
- Configure TCP/IP IPV4 or IPV6 properties based on your needs, you can use different IP address schema, domain controllers will register their new IP addresses and their DC related DNS records into DNS on the first reboot.
- Reboot the DC into regular mode
- Wait for SYSVOL to become available ,
- login to DC with Domain administrator privileges
- Perform an authoritative SYSVOL restore Set BurFlags to D4
- Click Start, and then click Run.
- In the Open box, type cmd and then press ENTER.
- In the Command box, type net stop ntfrs.
- Click Start, and then click Run.
- In the Open box, type regedit and then press ENTER.
- Locate the following subkey in the registry:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\NtFrs\Parameters\Backup/Restore\Process at Startup
- In the right pane, double-click BurFlags.
- In the Edit DWORD Value dialog box, type D4 and then click OK.
From command prompt type “net Share” to verify SYSVOL is shared.
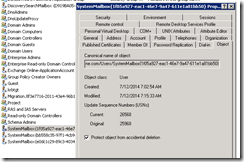
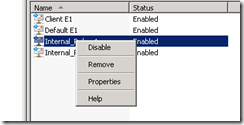
Perform metadata cleanup ( Windows 2008 use ADUC ) or NTDSUTIL , if you are in large environment using ADUC is much faster, simply locate the DC computer object and select delete.( Related Link )
Tip: If you leave the FSMO Role holders to last to FSMO role DC’s will force FSMO Seizure to surviving DC ( one last step to worry about seizing the FSMO Roles)
- Reset machine account twice
- Reset the krbtgt account password twice
- Reset all trust passwords
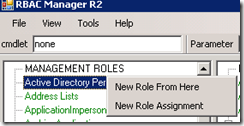
- Seize the FSMO roles if you have not done it already
- Delete all orphan KCC replication connections
- Clean up DNS, Name Servers , Forwarders , Stale CNAME, Glue records, delete them all.
- Promote second DC on the root domain, if you have single label domain name space at this point you would DCPROMO other DC’s.
- On the Child Domain Restore First Writable Domain Controller
- Log into DSRM mode
- Perform all initial steps done on the previous restore
- Make sure TCP/IP properties Primary DNS for Child Domain controller is pointing to Root DC.
- Reboot restored Child Domain controller into regular mode.
- Wait for SYSVOL to be available
- Log into DC
- You need to set BurFlags to D2 on the child domain controller , if you wont do this SYSVOL folder will disappear after some time.
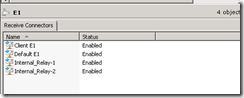
- Use RepAdmin to make sure replication from Child to Parent is working
- Perform Metadata Cleanup
- Perform FSMO Role Seizure.
- Check to make sure DNS comes up.
- Cleanup all stale CNAME,A , GLU, RDNS entries
- Make sure DC’s are stable
- Start planning your application servers recovery and have fun (-:
DCDiag and RepAdmin are two of the most powerfull command line tools use them.
dcdiag /V /C /D /E /s:DCname > C:\temp\DcDiag.txt
Oz Casey, Dedeal ( MVP North America)
MCITP (EMA), MCITP (SA)
MCSE 2003, M+, S+, MCDST
Security+, Project +, Server +
http://smtp25.blogspot.com/ (Blog)
http://telnet25.wordpress.com/ (Blog